Have you ever needed to capture network traffic on a Linux server and wanted to send the capture data directly to your Windows PC running Wireshark?
Capturing and inspect network traffic with “tcpdump” is usually painful. Of course, “tcpflow” can be a very useful tool, but is not always enough to sniff in a console. Wireshark is always a better option when it’s time to debug and troubleshooting communication problems.
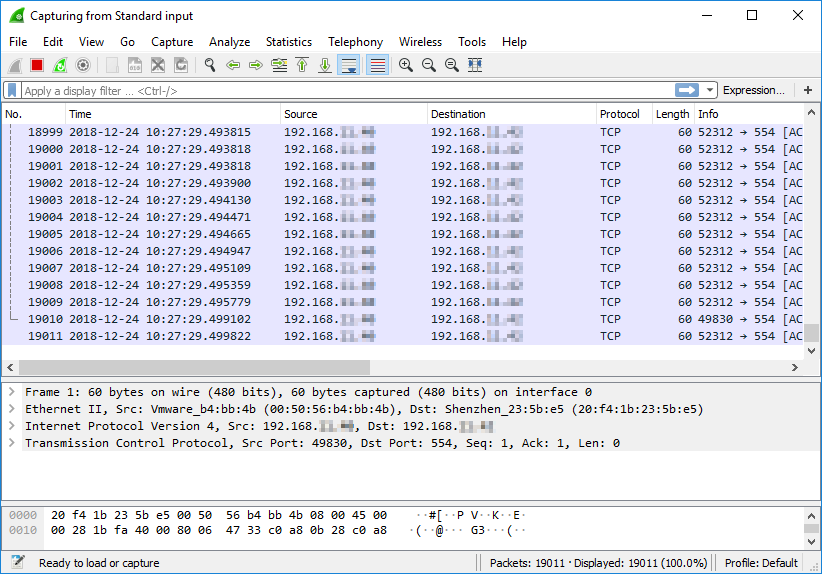
An option is to stream the captured traffic to another machine with Wireshark and dissect the packets in their layers, fields, etc.
What if your Wireshark machine is based on Windows? Simple – you need “plink.exe“, which is part of PuTTY.
Prerequisites
- Windows machine with PuTTY Installed [ Download ]
- Windows machine with Wireshark Installed [ Download ]
- SSH Key for password-less connectivity (Optional ~ Recommended)
Instructions on Settings up SSH Keys
Once you have the above prerequisites setup, use the below Windows batch script template to create a connection to your remote Linux server via SSH and capture the network traffic.
First, create a new file on your PC with the extension .cmd and copy the below script into it and save it.
@ECHO OFF
:: Application Paths
SET plink_bin="C:\Program Files\PuTTY\plink.exe"
SET wireshark_bin="C:\Program Files\Wireshark\Wireshark.exe"
:: Remote SSH Host Information
SET host="{{host-ip-address}}"
SET host_nic="{{host-interface}}"
SET ssh_user="root"
SET ssh_key="{{putty-ssh-ppk-key}}"
::
:: Do not change anything below this line
::
%plink_bin% -ssh -i %ssh_key% %ssh_user%@%host% "tcpdump -ni %host_nic% -s 0 -w - not port 22" | %wireshark_bin% -k -i -
Next, you will need to replace the the variables for your SSH host connection. These are located in the SET commands just below the “Remote SSH Host Information” settings.
Example connection to our EVE-NG virtualization lab server
1 – Get the network interface information, from the remote server, that we want to capture traffic on.
root@eve-ng:~# ifconfig pnet0
pnet0 Link encap:Ethernet HWaddr 00:0c:29:4f:f7:0b
inet addr:192.168.11.67 Bcast:192.168.11.255 Mask:255.255.255.0
inet6 addr: fe80::20c:29ff:fe4f:f70b/64 Scope:Link
2 – Edit the MS Batch Script with the variables. For the “ssh_key” value, enter the full path to your .PPK (Putty Private Key) file.
3 – Save and Execute the CMD file. Wireshark will automatically open on your PC and the capture will start.
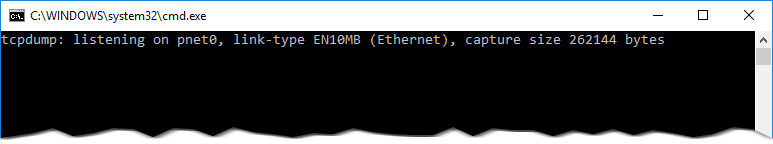
Do not close the CMD window that opens up. This will stop the capture process and disconnect the plink session to the remote server.
.